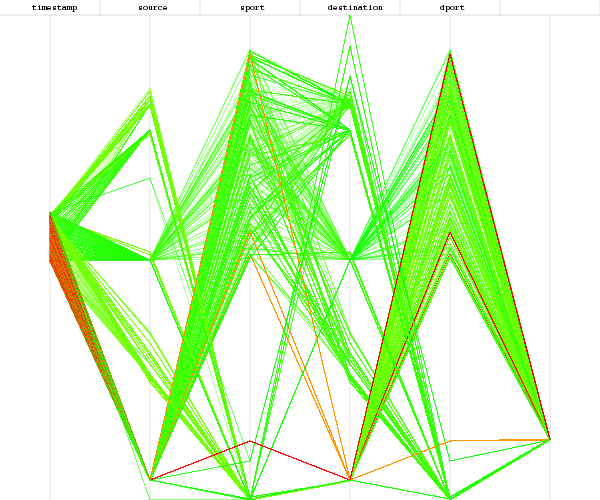
Researchers are monitoring a massive spam campaign from the Zbot/Zeus botnet purporting to be instructions for signing up for H1N1 vaccinations with the U.S. Centers for Disease Control (CDC).
Clicking on a link in the spam messages takes potential victims to a CDC-look-alike page where they are instructed to download a “profile” — a form to get the vaccination. The downloaded file makes their machines part of the Zbot (or Zeus) botnet. Those who don’t click on the link can also get infected by an IFRAME exploit on the page that uses vulnerabilities in unpatched Adobe applications.
Email security company AppRiver said it was seeing about 1.1 million such spam messages per hour Tuesday. That rate had slowed to about half that by yesterday, they said.
Story here.
Tom Kelchner
 I’m happy to say that in the
I’m happy to say that in the