In spite of the polarized, poisonous atmosphere in Washington, D.C., generated by President Barak Obama’s health care reform campaign, two Senators from very opposite ends of the political spectrum are co-sponsoring a bill to fight international cybercrime.
U.S. Senators Kirsten Gillibrand (D-NY) and Orrin Hatch (R-UT) have cosponsored a bill aimed at fighting international cyber crime: the International Cybercrime Reporting and Cooperation Act.
If enacted into law, the bill would give the U.S. government the power to help countries that need assistance in their fight against cyber crime. It also gives the U.S. government the power to cut off financial assistance to countries that don’t crack down on net criminals.
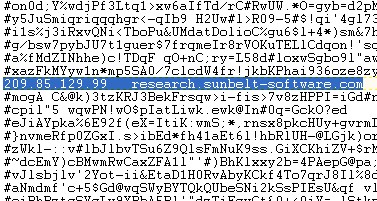
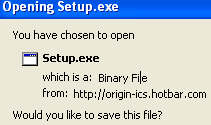
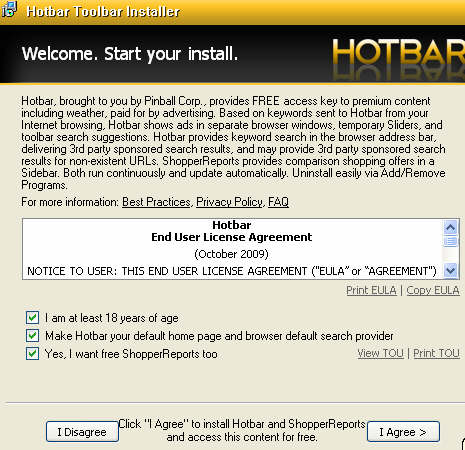
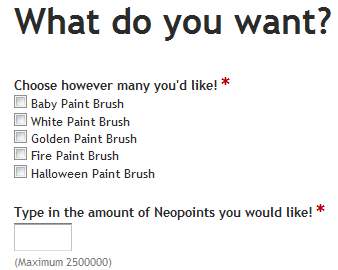
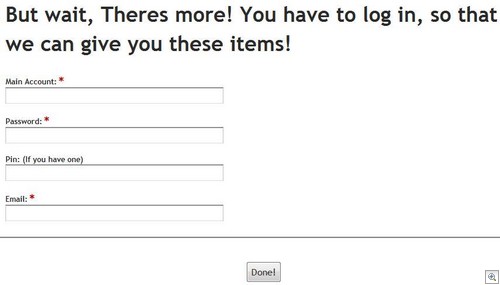
A wide variety of Internet criminals currently rely on bullet-proof servers in countries where their crimes are tolerated. It is believed that in some countries cyber crime is protected by corrupt governments or seen as a source of income for the country as long as the victims are all foreigners.
U.S. criminal investigators and those of other countries who have evidence to shut down criminal operations often get no cooperation from law enforcement groups in countries where the crime is tolerated. Russia, many eastern European countries, Nigeria and China traditionally have topped the list of non-cooperating countries.
In their news releases on the introduction of the bill, the two senators said:
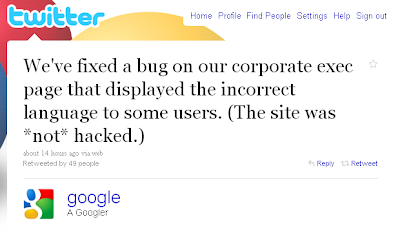
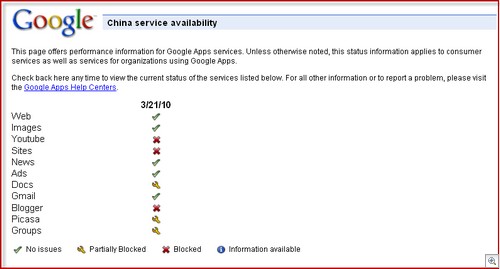
“Earlier this year, hackers in China launched a large, sophisticated attack on Google and other American businesses. A conservative estimate from the Government Accountability Office (GAO) estimates that in 2005 U.S. businesses lost $67.2 billion as a result of cyberattacks. Since then, attacks have dramatically increased. The global economy overall lost over $1 trillion in 2008 as a result of cyber attacks, according to studies by McAfee, Inc.”
The bill would:
— Establish an annual presidential report in which the President would assess the extent of cybercrime in each country as well as the country’s efforts to fight it and protect consumers and online commerce. It also would report on multilateral efforts against cybercrime.
— Prioritize programs designed to combat cybercrime to help countries with little information and communications technology in order to stop them from becoming cybercrime havens.
— Provide assistance to improve finance or telecommunications infrastructure in countries that need it in order to combat cybercrime.
— Identify countries of cyber concern: those with a pattern of cybercrime against the U.S.
— Identify the countries that don’t deal with cybercrime “through investigations, prosecutions, bilateral or international cooperation, or appropriate legislation.”.
— Establish an action plan to help governments of high cyber-crime countries fight it.
— Penalize countries that fail to meet benchmarks in their action plans by cutting off financing, preferential trade programs, or new foreign assistance, as long as the penalties don’t limit projects to fight cybercrime.
— Have the Secretary of State designate a senior official to coordinate the international fight against cybercrime and appoint employees at key embassies to focus on cybercrime policy.
We wish the Gentleman from Utah and the Lady from New York success.
Sen. Gillibrand news release here.
Sen. Hatch news release here.
Tom Kelchner