Hype and hysteria is normal in the AV business. After all, it’s been an intrinsic part of the business model since the Michelangelo virus. However, I get quite concerned about stuff like this when it could be used as a justification for war. South Korea, already on pins and needles because of its bellicose and nutty northern neighbor, is now suspecting that same country of launching a “cyber” war.
This is nuts.
I know of not a shred of evidence that this bot is from North Korea. It would take considerable research to ascertain the original source (the relevant IPs to the malicious code are in several places — Florida and Germany).
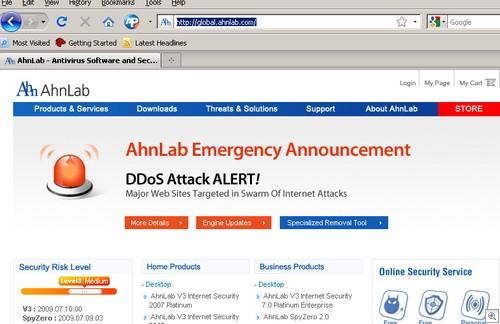
What happened here is trivial stuff in the security world: A bot got on between 60,000 to 100,000 PCs, and started launching DDoS attacks.
BFD. This hasn’t happened before? Russian politicians have to run their political campaigns on social networks because they are so used to being DDoSed during political campaigns. This is common stuff in the malware world.
Through underground channels, one can contact a botmaster (someone who “owns” all these infected machines), and pay them to DDoS whomever. It’s a felony, but it doesn’t mean it doesn’t happen. Or, one can gain control of a command and control (C&C) server and start DDoSing. This is what that kid who was DDoSing CastleCops did — he found a C&C by accident (they are out there, we’ve stumbled upon them not a few times in our research), went to his local library and started DDoSing CastleCops.
And no, one does not have to run out and frantically buy AV software. MyDoom and its variants are well-known pieces of malware that have been out for years. Detections are pretty robust; if you have a recently updated AV product, you should be fine. And remember, millions of people aren’t infected with this bot — the count of infected systems is less than .01% of the entire PC universe.
A far, far more critical issue is the current DirectShow exploit — now that is something to get worried about.
(Incidentally, Brian Krebs is keeping a good tally of the situation, and also links to this excellent overview by Hauri.)
Alex Eckelberry