Actually your computer will run MUCH BETTER without this adware crap
Our researcher Adam Thomas found this little nugget while investigating a botnet that auto installed FLV Direct Player. As an added bonus, the player bundles Zugo Search adware on victims’ machines. FLV Direct is available freely on the web. The bot, however, uses an AutoIT script to script through the installation screens so the victim never sees the install:
It also changes the victim machine’s home page to bing.zugo.com.
Apparently this is some kind of affiliate operation – the malefactor affiliates get paid for installing LoudMo adware on the machines of unknowing victims and they just decided to do it wholesale with a botnet.
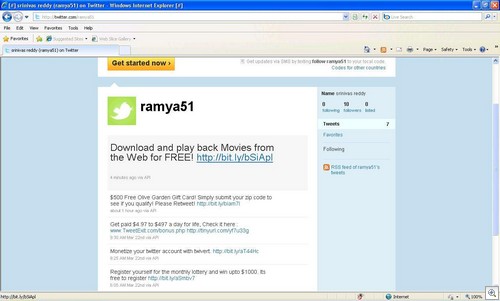
Affiliates also are spamming heavily on Twitter (and who else knows where else) trying to get people to install the FLV Player:
The FLV site (http://www.loudmo.com/products/flv/) describes their program:
“Use this free FLV Player to promote and target a wide variety of niches.
“Both affiliates and users will benefit from this free flash media player. Affiliates can boost revenue with the pay-per-install compensation method, while users will enjoy playing and saving flash videos from various tube sites. There is a completely transparent downloading process and the FLV player is easy to uninstall.
“FLV Player is a media player for MPEG-4 and Flash Videos (FLV). Most video sites on the web (including YouTube) stream FLV content. With the FLV Player, we offer an easy way to download and enjoy this content on your desktop. FLV Player comes with no viruses or spyware, and at just 2.12 Mb, it’s a quick download.”
One FINAL gimmick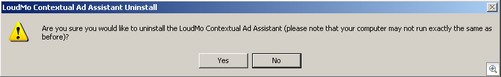
When victims uninstall LoudMo, they get the above warning. Obviously it’s one last effort to scare them into leaving the adware on their machines.
VIPRE detects the player as Adware.Win32.FLVDirectPlayer (v) and the included adware as Zugo Ltd (v) or Zugo.
Thanks Adam and Matthew and Eric.
Tom Kelchner