Today, our friends at Trend Micro blogged about a new attack vector using Microsoft Word documents. We saw this as well last week, and have written a detection for the dropped trojan.
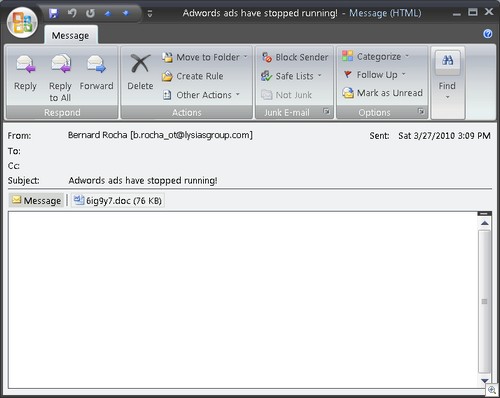
It’s not just a “lawsuit” that’s being spammed, we also picked up another form of this attack in our honeypots over the weekend:
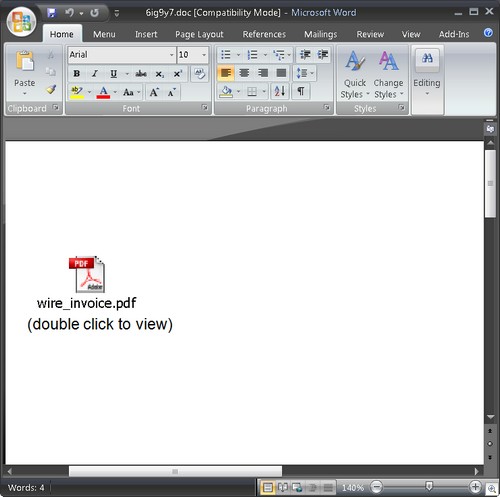
When you open the Word document, you see a “PDF”, but it’s actually not. It’s a JPG, which links to an executable.
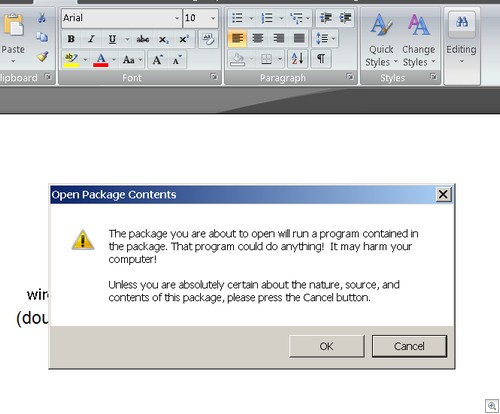
In Word 2007, it’s kind of like the Amish virus: The user has to really want to get infected.
Latest VirusTotal detection here.
Alex Eckelberry