ComputerWorld is carrying a good feature story on public wi-fi security practices that is worth reading whether you’re a road warrior who needs a place to work or just a regular schlep looking for Internet access and a caffeine buzz. (“Hot spot dangers: That Internet cafe could cost you way more than a cup of coffee”)
When you use a public Internet connection of any kind, you simply don’t know who is sniffing the network, looking for login information, personal data or sensitive documents. It would be a really good idea just not to work without an encrypted connection or do your banking or any transaction using credit/debit cards from these public places.
The ComputerWorld article has some interesting numbers from a 2009 Ponemon Institute study of security breaches suffered by 45 organizations. According to the study, “Cost of a Data Breach.” It said the cost of a data breach per compromised record was $204, up from $202 in 2008. The total cost per break-in was over $6 million.
If you’re communicating with your company network through a public hot spot the basic drill for beginners is:
— be aware that your unencrypted Internet traffic CAN be sniffed by anyone with the expertise and a connection to the wi-fi network
— be sure all software and operating system updates have been installed on your machine
— connect through your company’s VPN
— use air cards to avoid the dangers of a public network entirely if possible.
Encryption on the cheap
At minimum, if you MUST use a public hot spot and are not using an encrypted connection, it is fairly easy to encrypt the documents from many common applications before you email them. You can contact the recipient by phone and give him or her the password, or simply agree on a password in advance.
For Microsoft Word, Excel and PowerPoint:
Tools | Options
Click on the “Security” tab.
Fill in the edit box “Password to open”
By clicking on the “Advanced” button, you can choose an encryption scheme and key length. Choose a scheme that allows a 128 bit key (see below.)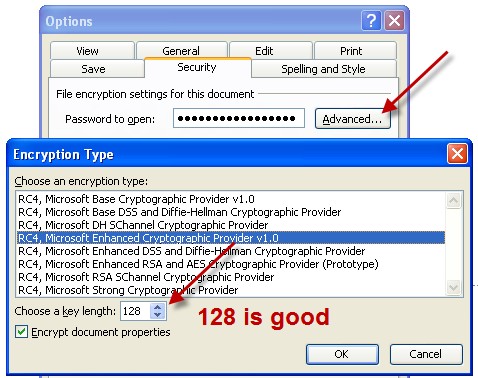
If you’re expecting to send encrypted documents to someone while you’re on the road, it might be a good idea to do a dry run with a test document before you leave to make sure your systems are compatible and everyone knows how to do it.
There also are compression utilities that allow you to create encrypted archives with passwords. In the common WinRAR utility go to: File | Set default password
Enter your password.
Can this encryption be cracked? Yes, if the malicious operator who sniffs the files has some very considerable resources. But it isn’t especially easy. At least your data won’t be low-hanging-fruit.
Tom Kelchner
Update 04/22:
As Phil has pointed out in the comments (below), the RC4 encryption used in Office 2003 and before is no longer safe. See our April 22 blog entry: “A note (correction) from the crypto world on Internet Café security.”

