This latest Facebook scam seems to have been rattling around for a few weeks now, directing you to malware from hacked websites hosting the rogue files. There also appear to be various Facebook application pages offering up the same dubious content.
Typically, the scam involves sending messages to Facebook users from compromised accounts similar to this one:
For those of you with images switched off (and that probably isn’t good where my writeups are concerned, as I tend to stuff each one with a million of the things), the message reads: “Foto 😀 apps(dot)facebook(dot)com/photobf/index(dot)php”.
Not a lot of sophistication there, but it doesn’t really take much to get people clicking. Downloading the file and running it will result in you sending your friends more “Foto” related spam and the whole process begins again.
Some users report the messages appearing on their walls, while others have screenshots of messages popping up in their chat applications. Either way, regardless of how the link is delivered the end-user will find themselves on a page containing nothing but a tantalising message regarding their photo hunt.
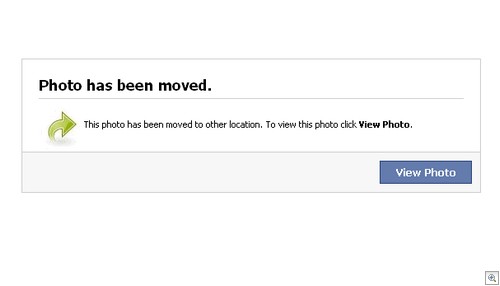
Yes, unfortunately the photo the end-user is trying to view “has been moved”. Never fear, clicking the “View Photo” button will reveal a photograph. Right?
Actually, no. The end-user is asked to download a file claiming to be an image.
Well, that seems suspicious. I wonder what happens if we ask Windows to stop hiding default file extensions…
You know, I think we rumbled their cunning plan. Infections spamming out malicious links isn’t anything new (in fact, the filename used here pops up at least as far back as 2009!) but people will still fall for it so it pays to be on your guard.
So far, postings on the web indicate the following app pages were involved (all of which are now deactivated):
apps(dot)facebook(dot)com/bestfunnypicever
apps(dot)facebook(dot)com/costumphotos
apps(dot)facebook(dot)com/photobf
apps(dot)facebook(dot)com/hahahahahahh
The good news is that many of the compromised websites hosting the infection file are being taken offline, Facebook are shutting down rogue application pages quickly and the VirusTotal score is coming along nicely with a 32/43 detection rate – we detect this one as Trojan.Win32.Generic.pak!cobra.
Let’s hope decent detection rates along with a growing awareness that random photo viewing requests may not be what they seem will put this one out to pasture for good.
Christopher Boyd