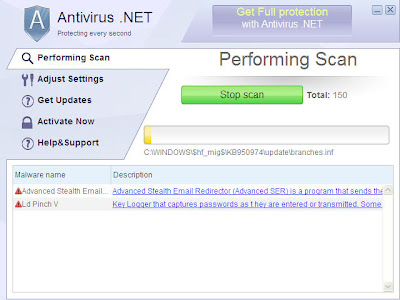
Sure, I’ll buy Antivirus.Net.FakeSpyPro rogue.
Yesterday on the GFI Rogue Blog we reported finding the Antivirus.Net rogue security product (FakeSpyPro family).
Today, researcher Patrick Jordan came across the browser hijacking mechanism that the rogue installs to trick a victim into making a purchase. After the “scan” is performed, this is the only page that a browser user will see:
(Click on graphic to enlarge)
The fractured English – “There might be an active spyware running on your computer” is one giveaway that this isn’t genuine.
Thanks Patrick.
Tom K