Reported in Codefish. We checked out this Trojan and it’s not very friendly.
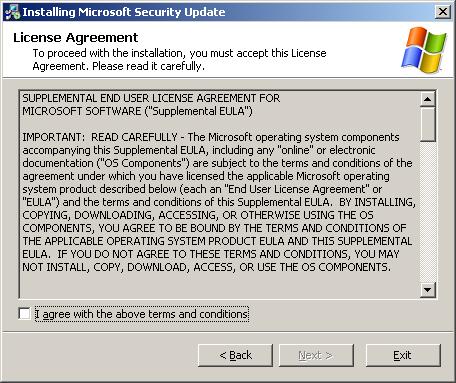
Here is what the email looks like::
Microsoft Security Bulletin MS05-039
Vulnerability in Plug and Play Could Allow Remote Code Execution and Elevation of Privilege (899588)
Summary:
Who should receive this document: Customers who use Microsoft Windows
Impact of Vulnerability: Remote Code Execution and Local Elevation of Privilege
Maximum Severity Rating: CRITICAL
Recommendation: Customers should apply the update immediately.
Security Update Replacement: None
Caveats: None
Tested Software and Security Update Download Locations:Affected Software:
•
Microsoft Windows 2000 Service Pack 4 – Download the update
•
Microsoft Windows XP Service Pack 1 and Microsoft Windows XP Service Pack 2 – Download the update
•
Microsoft Windows XP Professional x64 Edition – Download the update
•
Microsoft Windows Server 2003 and Microsoft Windows Server 2003 Service Pack 1 – Download the update
•
Microsoft Windows Server 2003 for Itanium-based Systems and Microsoft Windows Server 2003 with SP1 for Itanium-based Systems – Download the update
•
Microsoft Windows Server 2003 x64 Edition – Download the update
Non-Affected Software:
•
Microsoft Windows 98, Microsoft Windows 98 Second Edition (SE), and Microsoft Windows Millennium Edition (ME)
Executive Summary:
This update resolves a newly-discovered, privately-reported vulnerability. A remote code execution vulnerability exists in Plug and Play (PnP) that could allow an attacker who successfully exploited this vulnerability to take complete control of the affected system. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights.
Conclusion: We recommend that customers apply the update immediately.
© 2005 Microsoft Corporation. All rights reserved.
Terms of Use | Trademarks | Privacy Statement


(“No virus found” means that the virus scanner did not detect it):
This is a report processed by VirusTotal on 12/12/2005 at 18:59:39 (CET) after scanning the file “Windows-KB899588-x86-ENU.exe” file.
| Antivirus | Version | Update | Result |
| Avast | 4.6.695.0 | 12.10.2005 | No virus found |
| AVG | 718 | 12.08.2005 | No virus found |
| McAfee | 4648 | 12.12.2005 | No virus found |
| NOD32v2 | 1.1319 | 12.12.2005 | No virus found |
| Norman | 5.70.10 | 12.12.2005 | No virus found |
| TheHacker | 5.9.1.053 | 12.12.2005 | No virus found |
| F-Prot | 3.16c | 12.09.2005 | security risk or a “backdoor” program |
| AntiVir | 6.33.0.61 | 12.12.2005 | TR/Luhn |
| Avira | 6.33.0.61 | 12.12.2005 | TR/Luhn |
| Panda | 8.02.00 | 12.12.2005 | Trj/Spy.Luhn |
| Sophos | 4.00.0 | 12.12.2005 | Troj/Dropper-BV |
| Symantec | 8 | 12.12.2005 | Trojan.Dropper |
| DrWeb | 4.33 | 12.12.2005 | Trojan.Sklog |
| BitDefender | 7.2 | 12.12.2005 | Trojan.Spy.Luhn.A |
| ClamAV | devel-20051108 | 12.12.2005 | Trojan.Spy.W32.Luhn |
| CAT-QuickHeal | 8 | 12.12.2005 | TrojanSpy.Luhn.a |
| Kaspersky | 4.0.2.24 | 12.12.2005 | Trojan-Spy.Win32.Luhn.a |
| VBA32 | 3.10.5 | 12.12.2005 | Trojan-Spy.Win32.Luhn.a |
| Fortinet | 2.54.0.0 | 12.11.2005 | W32/SpyLuhn.A-dr |
| eTrust-Iris | 7.1.194.0 | 12.11.2005 | Win32/Luhn!Spy!Dropper |
| eTrust-Vet | 12.3.3.0 | 12.12.2005 | Win32/Luhn.A |
Alex Eckelberry
(Hat tip to Sunbelt researchers Eric Sites, Eric Howes and Patrick Jordan)
