Our friends at Commtouch have blogged about something that is no surprise — spammers using compromised accounts vs. bots (their latest threat report is quite good and worth reading btw).
While compromised email accounts (hotmail, yahoo, gmail, etc.) are not new, there is a little more to it: There was a massive takedown of a major spam operation by Microsoft several months ago. This led to spam levels dropping to their lowest rate in three years. Gamechanger for the spammers. So what we’re likely seeing is a) the percentage of spam from compromised accounts increasing, because Rustock is out of the equation (the mix of compromised accounts vs. legitimate has changed) and b) it’s just getting harder to use botnets, so they’re going after compromising existing accounts. Since Commtouch didn’t publish data as to the raw actual numbers of compromised accounts vs. bot spam, it’s difficult to tell.
Nevertheless, bots are still out there. But compromised accounts gives spammers the ability to hijack the reputation of an existing user and service (hard to blacklist all of Hotmail, for example). You could spoof an email to look like it’s from gmail or Hotmail (and there is a lot of that), but that’s not nearly as powerful as a compromised account, because the IP ranges are trusted by spam filters, and generally, the sender is trusted by you (it could be a family member, or a friend).
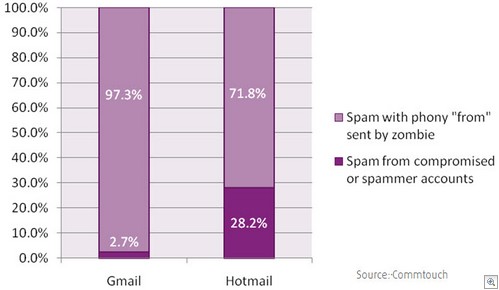
You can see in the chart below that Hotmail is more compromised than Gmail. Gmail spam is almost all spoofed — simply creating a fake gmail address in the From address — a poor way of getting by spam filters.
However, it’s not necessarily pharmacy ads and the like. There’s plenty of malwere. There’s also malicious links, which themselves can pose a greater problem, because malware is often caught going through an antivirus filter (either because of attachment policies or because the malware itself are caught). However, malicious links from a trusted sender present a far bigger problem.
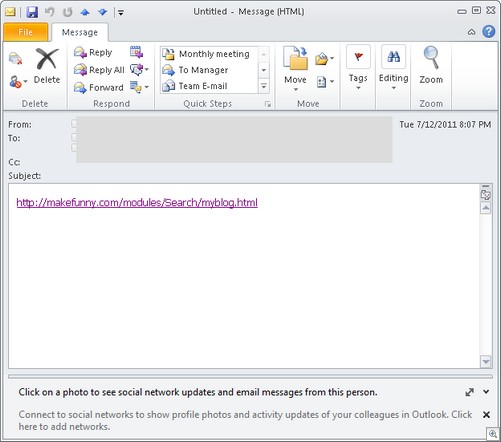
For example, here’s a current spam run using a compromised Hotmail account we saw yesterday (they simply stole the user credentials), pushing a rogue antivirus product:
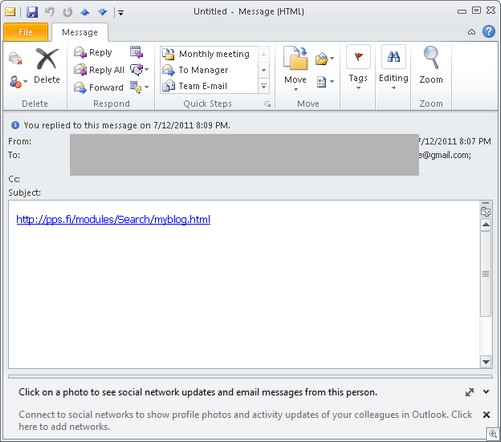
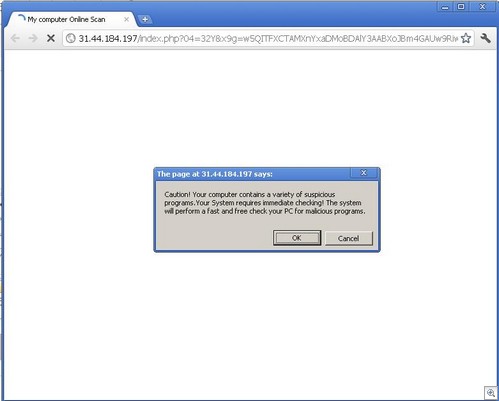
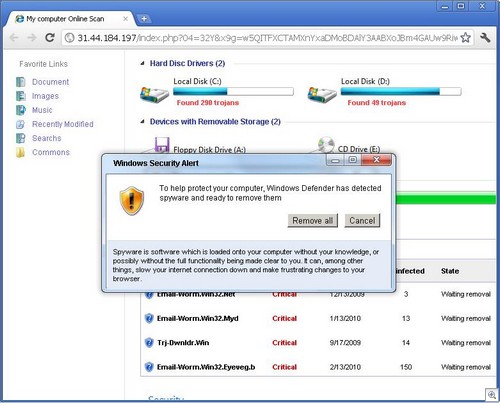
Same spam run, both with the same results – clicking on the link redirects one to a page that looks like this:
This pushes a download of WinWebSec SecurityShield, with atrocious detection by AV vendors. So antivirus detection being awful in this case, the emphasis becomes on defense-in-depth. A good spam filter may or may not help, because this email comes from one of your trusted senders and may be ignored, depending on your policies. A good web filter would certainly help significantly. And so on. However, since social engineering is at play here, education is of tremendous importance.
Alex Eckelberry