Botnet controllers are getting quite sophisticated. And as we can here, even visually appealing.
Check out this botnet controller that our Adam Thomas just found.
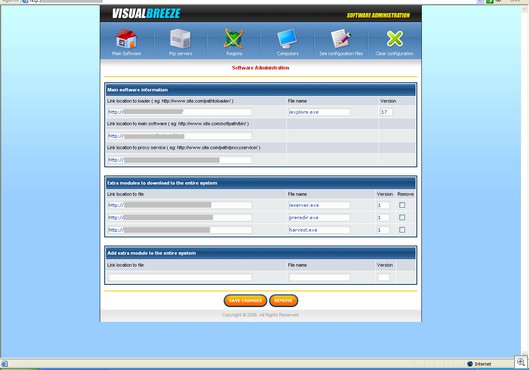
Here’s the main control page:
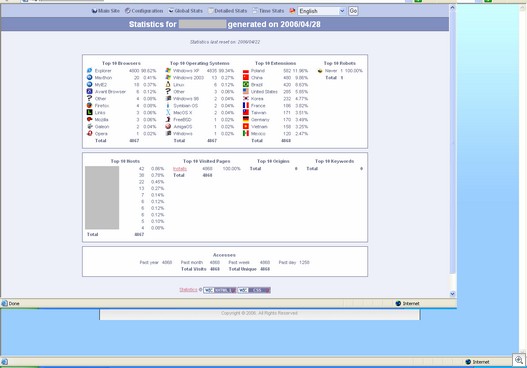
Here’s the reports page.
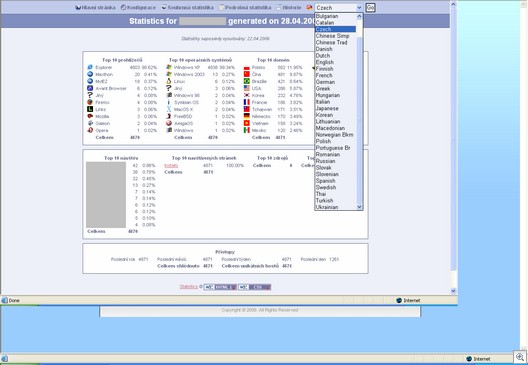
It’s even translated into multiple languages, as not all hackers speak perfect English:
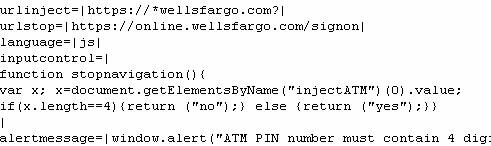
There’s also some handy-dandy code we discovered there for html code injection, which is used for phishing.
Then, we found the stolen data. Credit card numbers, passwords, the works, from countries all over the world. Sick stuff.
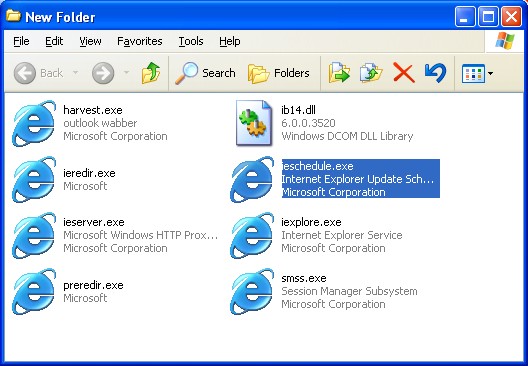
The botnet lives off a bunch of really ugly malware, with the following file names (Virustotal links included).
iexplore.exe
ieschedule.exe
ib14.dll
smss.exe
ieserver.exe
preredir.exe
harvest.exe
ieredir.exe
Current virus detection is pretty weak on this set of malware.
Of course, the trojans look perfectly legitimate:
Alex Eckelberry