Sans just recommended removing certain IP ranges from block lists:
Update:
Based on feedback from Intercage customers, we no longer recommend to block them. Please let us know if you see any problems from 69.50.160.0/19 and we will try to facility contact and a resolution.
Link here.
The IP ranges in question are:
InterCage Inc.: 69.50.160.0/19 (69.50.160.0 – 69.50.191.255)
Inhoster: 85.255.112.0/20 (85.255.112.0 – 85.255.127.255)
While we rarely disagree with our friends at SANs, we do NOT recommend removing these ranges, at least not 69.50.160.0/19. This is a live bad range.
Examples:
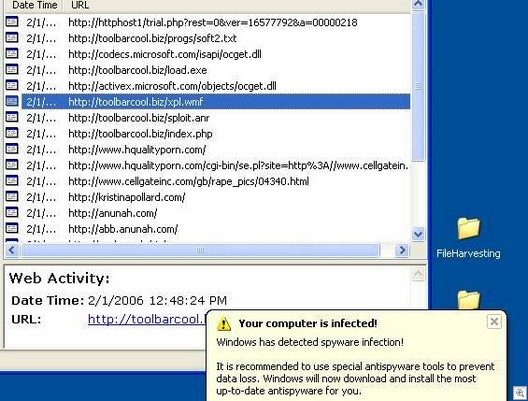
kristinapollard.com 69.50.188.36
Andy Placid
London GB
placid @ treffend.com
Or this one:
And let’s not forget the very evil Vcodec, http://www.vicodec(dot)com (69.50.160.61), which is responsible for SpyAxe, SpyStriker, desktop hijacks, pop-up advertising, toolbar installs, and all that fun.
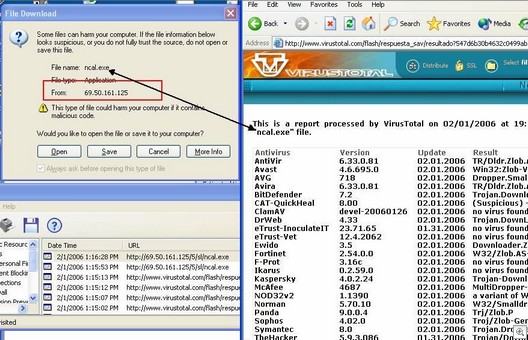
As regards the 85.255.112.0/20 range, the IP range is hosed with live files and the sites that look normal also make calls to the 195 and 85 of the Russian servers:
- dirty-rape(dot)com calls in the rotational 85.255.113.22 IP that will end up running a wmf exploit and infestation.
- 69.50.161.169 dirty-rape.com calls in Iframe:85.255.113.22/inc/yfuzz.html
- 85.255.113.22/inc/yfuzz.html redirects to: 85.255.113.10/?to=yfuzz&from=in
- 85.255.113.10/?to=yfuzz&from=in calls: 85.255.113.83/users/fill/web/count.php?id=yfuzz
- 85.255.113.83/users/fill/web/count.php?id=yfuzz in Iframe runs 85.255.113.83/users/fill/web/xxx.wmf
- The wmf calls to 85.255.113.84/users/smell/web/sex.
85.255.114.* is also a bad site (Wuster Ltd sites running wmf exploits).
However, 85.255.112.0/ to 85.255.112.255 may be clean.
Maybe SANS should recommend to blocking specific domains and IP address instead.
For example:
x-stories.org – 69.50.187.19
zlex.org – 85.255.115.227
85.255.116.213
85.255.117.51
And preferably these as well:
Noi.themovie.com that calls the x-stories.org – 69.50.187.19
Cleanchan.net – (formally fullchain.net) -195.255.177.21
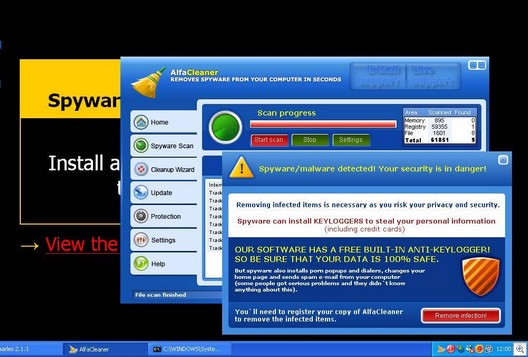
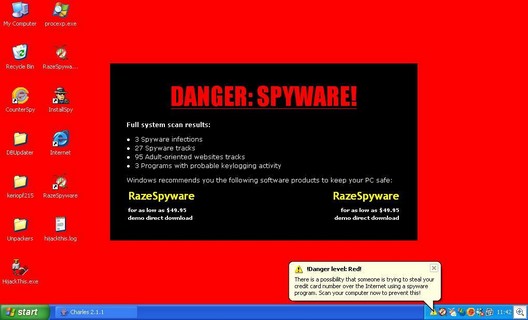
Or else people with un-patched machines are going to end up looking at this
or this, depending on the day and time:
Alex Eckelberry
(Thanks to Sunbelt researchers Patrick Jordan, Adam Thomas)