Remember the old kids’ mantra celebrating the arrival of summer? “No more pencils, no more books, no more teacher’s dirty looks.” Well, students may be stuck with that last one for a while longer, but the first two are about to become obsolete year ’round, at least in some school districts.
My local newspaper ran a story last weekend titled “Schools toss aside texts for e-books”. It seems several districts in our area are doing away with traditional textbooks altogether. And who can argue with the fact that electronic books offer several advantages? They’re a lot easier to keep up to date, and they certainly weigh a lot less than those fat hardbacks that students are used to lugging around. Kids can carry dozens of books with them in the same space and weight that one “real” book occupies. Link.
On the other hand, the digital nature of e-books also makes it easier to manipulate the content (a little rewriting of history, anyone?), and in order to use them, each student needs a computer. Asking parents to buy a laptop along with the rest of the list of first day school supplies seems a bit much, so the schools themselves are buying them and issuing them to students (at a cost of almost $900 each, according to the article). So, while students and teachers may be happy about this new way of doing things, already overburdened taxpayers may be less so (my property taxes for the public school district this year are well over $4000 – more than the taxes for the city, county, hospital district and community college district combined – and my district hasn’t even started buying laptops yet).
I’m a big advocate of teaching everyone to use new technology, but it seems to me there are some practical problems with this approach that haven’t been considered (or at least, haven’t been mentioned by reporters enamored with the “cool factor” of what the schools are doing). For instance, administrators expect to have to replace the laptops every four years. I wonder if that’s realistic, considering the fragile nature of portable computers combined with the rambunctious nature of school children.
What happens if a child drops his computer on the concrete and demolishes it a week after he gets it? Do the taxpayers get to pay for the repairs or replacement? Or do you require the parents to pony up, like when a child loses or damages a library book? What if they can’t afford it? Does the kid go without a computer (and thus without any of his textbooks) for the rest of the year? Will there be kiosks where kids who’ve lost their computers can stay after school to study?
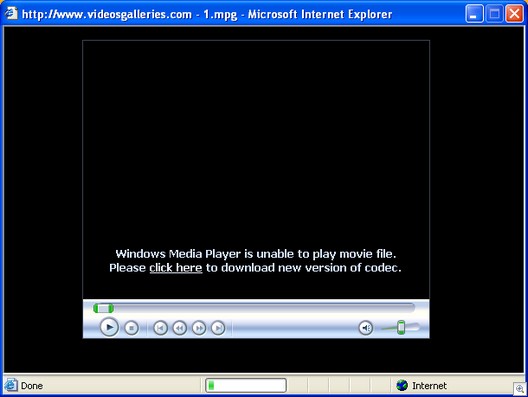
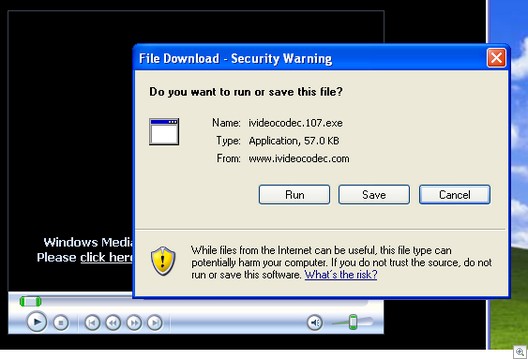
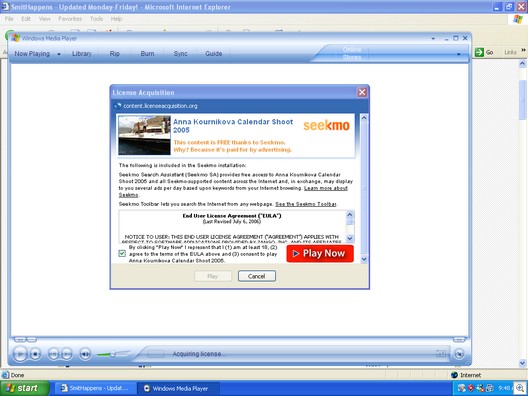
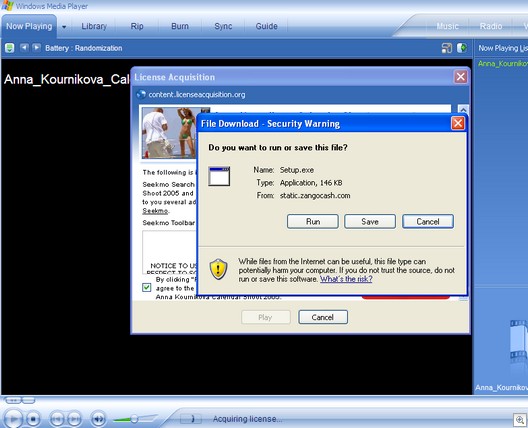
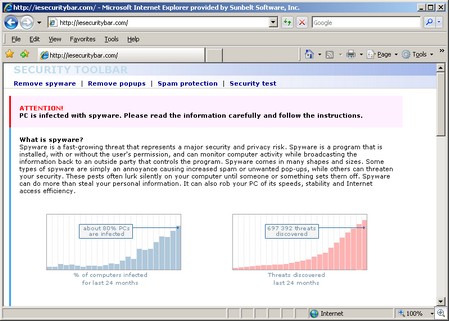
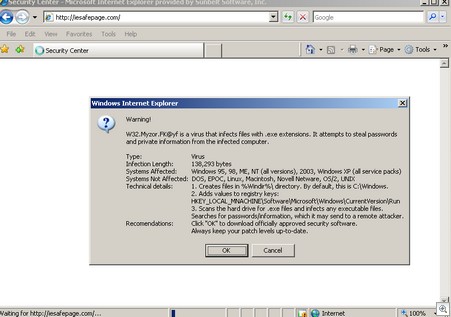
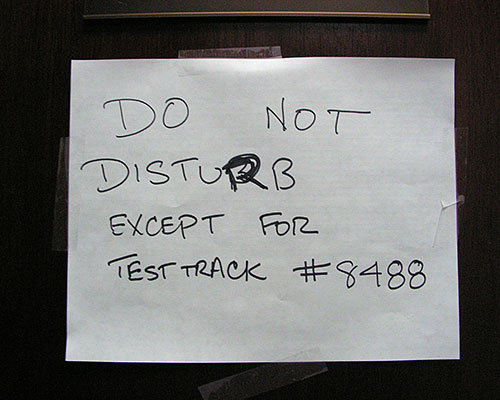
And as we all know, physical damage isn’t the only thing that can render a computer unusable. Kids love to experiment; when they inevitably delete the wrong files, install some sort of malware, or otherwise mess up the operating system so that their programs won’t run, who’s going to fix it? Will the schools also have to hire on-call tech support personnel to spend all their time troubleshooting software? Or will they teach each child how to format and reimage the hard drive whenever anything goes wrong?
If the children will be doing all or part of their work on the computers (which seems logical and is implied in the article), where will they save their documents? On removable media so that when/if the OS gets corrupted as described above, the data won’t be lost? Will the school issue flash memory cards or USB drives, too, for that purpose? What if a child labors for hours or weeks to complete a paper, and then the file gets corrupted (will “my computer ate my homework” fly any better than the old dog excuse?)? Or will they be required to print everything out? Maybe the school will buy everybody a printer, too?
The article stated that some teachers still order “back up” textbooks to keep in the classroom, but many don’t. Suppose there’s a power outage. Does all learning come to a halt? Or what if the power goes down for the evening in a particular neighborhood? Will the students in that neighborhood be excused for not doing their homework? No more studying by candlelight these days.
How locked down will the student laptops be? Will students be able to get online with them, or will they be configured to use as standalone machines only? If the former, how do you keep kids from using them to chat with friends, surf the web (perhaps to inappropriate sites), play computer games, etc. Or should you even try to restrict their use to learning only?
Of course, the student laptop programs are being pushed by computer vendors (what a surprise) and some educators. But what do you think? Will giving every student a computer better prepare them for life in the 21st century and bridge the digital divide? Or will such initiatives turn into budgetary monsters that will devour taxpayers with far too little return on the investment? Is there a better way to provide access to technology, such as installing the computers in the classrooms instead, or helping to subsidize home computers for students whose families can’t afford them, rather than giving a portable to every child?
Deb Shinder, MVP